Claude Code Leaked Source Code Analysis
While the leaked Claude Code's source is not readily runnable outside Anthropic's internal build pipeline, we reverse-engineered it to uncover undocumented hacks, hidden commands, and architectural patterns that let you push Claude Code further than the docs suggest.
How It Was Leaked
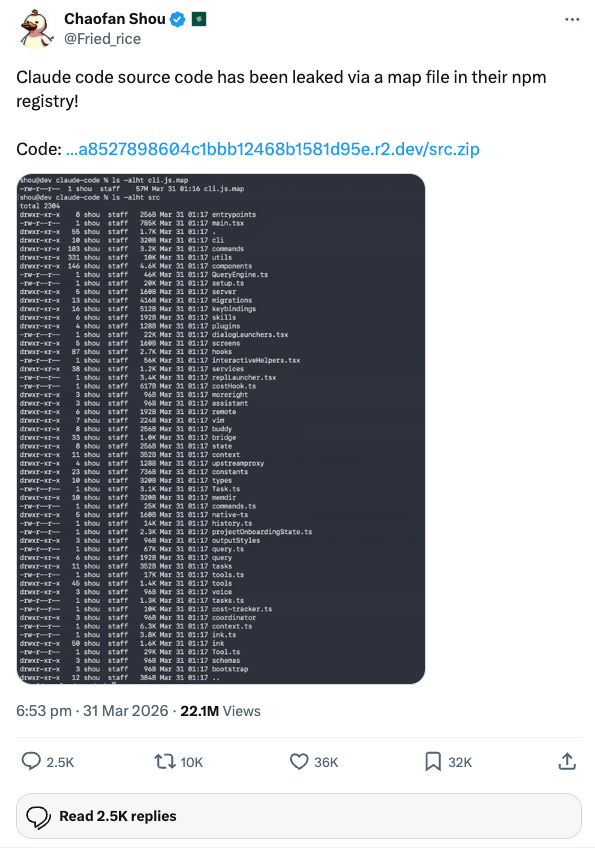
On March 31, 2026, Chaofan Shou (@Fried_rice) discovered and publicly disclosed that Claude Code's full, unobfuscated TypeScript source was accessible via a source map file in Anthropic's published npm package.
@Fried_rice
"Claude code source code has been leaked via a map file in their npm registry!"
The source map in the published npm package contained a reference to the full, uncompiled TypeScript source, which was downloadable as a zip archive from Anthropic's R2 storage bucket. The archive contained approximately 1,900 TypeScript/TSX files -- the entire Claude Code codebase before compilation and dead code elimination.
The source reveals the complete architecture: system prompt assembly, permission model, agent spawning, context compaction, memory system, feature flags, and more.
What Can You Actually Do With This?
- Reduce costs by up to 40% using undocumented environment variables that strip the system prompt, disable background tasks, and trigger earlier compaction
- Write better CLAUDE.md files by understanding exactly where your instructions land in the 15-section system prompt and what's already covered
-
Use hidden slash commands like
/rewind,/context,/stats, and custom/compactinstructions for targeted context management - Build custom agents with Haiku for cheap automation, define tools and permissions in simple markdown files
- Understand the security model from sandbox profiles to permission rules, so you know what Claude can and cannot do in your environment
- Master context management by learning how microcompaction, auto-compaction, and post-compaction file restoration actually work under the hood
How to Maximise the Source
-
Read
src/constants/prompts.tsfirst -- the single most valuable file. It shows exactly how Claude Code's behaviour is defined and what instructions the model receives - Apply the environment variable hacks from our Hacks & Optimisations page -- these are immediately usable and can significantly reduce your costs
-
Study the tool interface pattern in
src/tools/to build your own MCP servers and custom skills that match the exact internal format - Borrow the architecture patterns -- the custom Ink fork, agent spawning system, and permission model are reusable references for building your own AI-powered CLI tools
- Explore the feature flags to understand what Anthropic is testing internally and what features may ship next
Documentation Guide
Start with the practical content and go deeper as needed:
Hacks & Optimisations
The actionable stuff. Environment variables, CLAUDE.md tricks, cost reduction strategies, and hidden commands you can use right now.
System Prompt Assembly
How Claude Code's 15+ section system prompt is dynamically assembled, cached, and what your CLAUDE.md is competing with for attention.
Agent & Sub-Agent System
The multi-agent architecture: built-in agents, custom agent definitions, fork-based spawning, worktree isolation, and swarm coordination.
Permissions & Sandboxing
Seven security layers in the Bash tool alone, plus macOS Seatbelt sandboxing, permission modes, and enterprise MDM controls.
Context Compaction
Three levels of compaction (micro, auto, manual), the 9-section summarisation algorithm, and post-compaction file restoration.
Memory System
Four memory types, the MEMORY.md index with its 200-line hard limit, auto-extraction via forked sub-agents, and staleness caveats.
Feature Flags & Hidden Commands
Compile-time DCE flags, GrowthBook runtime A/B tests (codename: Tengu), and the full list of hidden slash commands.